Nobody planned for this.
When companies like Amazon, Google, Microsoft, and Oracle built their data centers in the UAE and Bahrain, they ran risk assessments for power failures, earthquakes, cyberattacks, and hardware failures. They built redundant power systems. They installed fire suppression equipment. They hired security guards and installed perimeter cameras.
Not one of them planned for drone strikes.
For the first time in military history, private sector data centers came under deliberate physical attack. And when it happened, it did not just affect the companies whose buildings were hit. It sent shockwaves through the entire global technology industry—forcing every CIO, every infrastructure head, and every enterprise IT team on earth to ask a question they had never seriously considered before: Is our data center a war target?
In 2026, the answer — for more companies than anyone expected — is yes.
Table of Contents
- The Full Timeline — Every Attack, Every Threat, Every Escalation
- What the Attacks Actually Destroyed — The Real Damage
- The 29-Target List — Which Companies Iran Has Threatened
- Why Tech Companies Are Now Legitimate Military Targets
- Global Business Impact — Who Got Hurt and How Much
- The $64 Billion Problem — What This Means for Data Center Investment
- What “Data Center War Target 2026” Means for Indian Enterprises
- The New Rules of Data Center Security After 2026
- How One World Logix Helps You Move Infrastructure to Safety
1. The Full Timeline — Every Attack, Every Threat, Every Escalation
The story did not begin on March 1. It began on February 28, 2026, when the US and Israel launched coordinated strikes on Iran. What followed was a rapid and unprecedented escalation into the digital domain.
What began on February 28, 2026 with coordinated strikes on Iran expanded beyond traditional military targets into the digital world — Iran responded not only with missiles and drones but also with attacks on digital infrastructure and direct threats to global technology companies.
Here is the complete timeline:
February 28, 2026 — US and Israel launch coordinated military strikes on Iran. The conflict begins.
March 1, 2026 — Before dawn, Iranian Shahed drones struck two Amazon Web Services data centers in the United Arab Emirates. A third commercial data center in Bahrain was hit. This is the first time in history a nation deliberately targeted commercial data centers during wartime.
March 11, 2026 — A strike hit a data center linked to Bank Sepah in Tehran that contained salary data for the IRGC and the Iranian army, disrupting salary payments to Iranian military elements and taking online banking temporarily inoperable. Both sides are now hitting each other’s digital infrastructure.
March 12, 2026 — An IRGC-affiliated news outlet published a list of 29 tech targets Iran plans to strike across Bahrain, Israel, Qatar, and the UAE — including five AWS, five Microsoft, six IBM, three Palantir, four Google, three Nvidia, and three Oracle facilities.
March 31, 2026 — Iran state media issued a statement that it will target American companies including Microsoft, Google, Apple, Meta, Oracle, Intel, HP, IBM, Cisco, Dell, Palantir and Nvidia.
April 1, 2026 — A second Iranian drone strike hits an AWS data center in Bahrain. Fire breaks out.
April 2, 2026 — Iran claims it has struck an Oracle data center in Dubai.
April 2026 — Iran released a video showing an image of a globe, then zooming in on the Stargate data center in the UAE with the message “nothing stays hidden to our sight, though hidden by Google.” Stargate is a $500 billion joint venture between OpenAI, SoftBank, and Oracle.
The message from Iran is now unmistakable: no data center in the region is off limits.

2. What the Attacks Actually Destroyed — The Real Damage
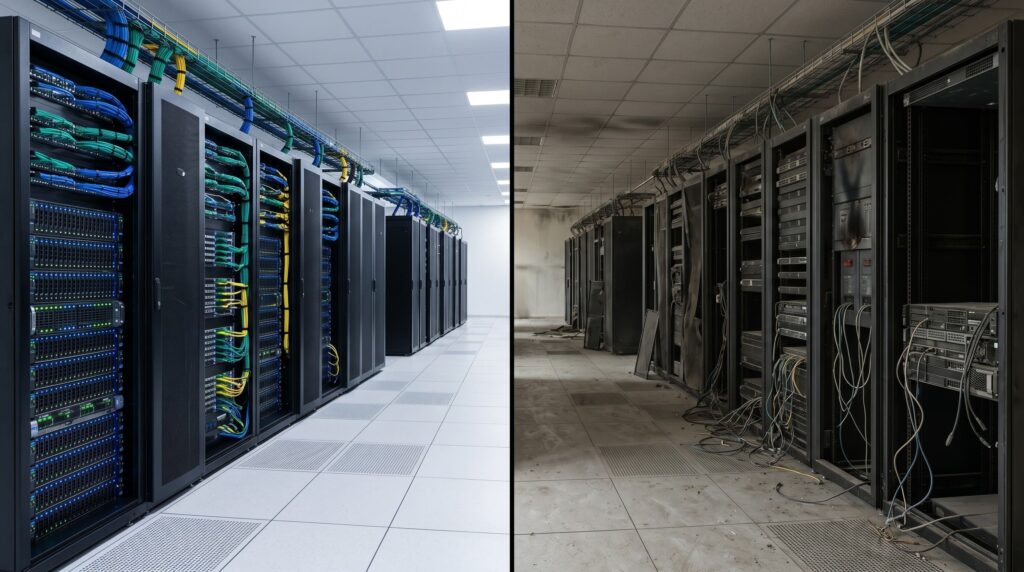
The physical damage from the March 1 strikes was more severe than most news reports conveyed.
AWS’s UAE region — ME-CENTRAL-1 — operates across three availability zones, three physically separate locations designed so that if one goes down, the others keep everything running. The March 1 strikes took out two of the three zones simultaneously. The third zone alone could not carry the load.
The strikes caused structural damage, disrupted power, and triggered fire suppression systems — highlighting vulnerabilities in physical plant design that were previously theoretical.
The services that went offline included EC2, S3, DynamoDB, AWS Lambda, RDS, Kinesis, CloudWatch, and the AWS Management Console. These are not peripheral services. They are the core infrastructure that thousands of businesses across the Middle East depend on for every transaction, every customer interaction, and every internal operation.
The businesses that reported significant disruptions include Abu Dhabi Commercial Bank, Emirates NBD, First Abu Dhabi Bank, payment platforms Hubpay and Alaan, Snowflake, and Careem — the Gulf region’s largest ride-hailing platform.
AWS took the extraordinary step of waiving all usage charges for the ME-CENTRAL-1 region for the entire month of March 2026. That decision — worth hundreds of millions of dollars — tells you everything about how serious the damage was. AWS was admitting it could not deliver the service its customers had paid for.
Recovery, AWS warned, would be prolonged given the nature of the physical damage involved. You cannot reboot a building that has been hit by a drone.
3. The 29-Target List — Which Companies Iran Has Threatened
This is the part of the story that most enterprises have not fully absorbed.
Iran has not just attacked data centers. It has published a specific, named list of future targets. The list included facilities run by AWS, Microsoft, IBM, Palantir, Google, Nvidia, and Oracle across Bahrain, Israel, Qatar, and the UAE.
Think about what that means. If your business runs on AWS, Azure, Google Cloud, or Oracle Cloud — and has workloads in any of these regions — your infrastructure is on a published enemy target list.
Iran also threatened tech companies including Nvidia and Apple by name.
Iran’s Revolutionary Guard Corps followed up with a video threatening to bomb OpenAI’s $30 billion Stargate data center.
This is no longer theoretical risk analysis. It is a named, stated, publicly declared intention by a nation-state military force. The companies on that list — and their enterprise customers — need to treat it accordingly.
4. Why Tech Companies Are Now Legitimate Military Targets
Understanding why this happened is as important as understanding what happened. Because the “why” explains why this is not going to stop.
In an era when companies known for e-commerce, social networks, and search engines have also become close collaborators with militaries, server farms may now have the same status as factories building bombs and warplanes.
The US military has been using AI — hosted on commercial cloud infrastructure — for intelligence analysis, targeting decisions, and operational support in the Iran conflict. Data centres power AI by providing the computer power, storage and high-speed internet needed to train the models — making them a critical building block of AI capabilities at the national level.
When a data center processes both a bank’s transactions and a military’s targeting AI in the same building, international law becomes complicated. Scholars of international law say that when a military runs on the cloud, the cloud becomes a legal military target.
Iran made a strategic calculation: hitting AWS data centers in the UAE would simultaneously disrupt potential military AI operations, rattle the global economy, signal its reach to the Gulf states, and demonstrate that the US’s digital infrastructure is physically vulnerable.
Experts said attacks on data centers mark a “sea change in warfare” that will require new policies from governments and enterprises alike.
The era of data centers as neutral civilian infrastructure is over.
6. The $64 Billion Problem — What This Means for Data Center Investment
The attacks have not just disrupted existing infrastructure. They have fundamentally altered the calculus for future data center investment globally.
In 2025 alone, at least 25 data center projects were canceled in the US — a four-fold increase from the prior year — with one report identifying 16 major projects worth a combined $64 billion blocked or delayed. This was before the Iran strikes. The attacks have accelerated a trend that was already underway.
“The biggest takeaway is that physical resilience was taken for granted for the longest time, even in the Gulf states,” said Michael Deng, a geoeconomics technology analyst at Bloomberg. “This huge bet on the Gulf, itself, as this big AI hub outside the US and China is looking, in hindsight, like not a really great decision.”
For the data center industry, 2026 represents a forced maturation. The definition of a mature, resilient data center is rapidly evolving to include drone defense systems, reinforced physical structures, and supply chain independence for critical components.
Companies that built their Middle East strategy around the assumption that commercial data centers were safe from military action are now rebuilding that strategy from scratch. The question is no longer whether to diversify — it is how fast and where to.
7. What “Data Center War Target 2026” Means for Indian Enterprises
India sits in a unique position in this story. India is not a party to the Iran-US conflict. India’s data centers are not on Iran’s published target list. And India has significant, growing domestic data center capacity in Mumbai, Pune, Bengaluru, Chennai, and Hyderabad.
This makes India — from a geopolitical risk perspective — one of the most attractive data center locations on earth right now for enterprises looking to move infrastructure out of conflict-risk zones.
But Indian enterprises are not just potential beneficiaries of this shift. Many are also directly exposed:
Any Indian company with cloud workloads running in AWS ME-CENTRAL-1 or ME-SOUTH-1 was affected by the outages. Any Indian company with physical servers or IT infrastructure in UAE or Bahrain offices is sitting in an active conflict zone. Any Indian IT services company with clients in the Gulf is having urgent conversations about business continuity right now.
The practical implications for Indian enterprises are clear: infrastructure in the Middle East needs a migration plan, a backup, or both. And that plan needs to exist before the next attack — not after.
8. The New Rules of Data Center Security After 2026
Prior to 2025, risk assessments for data centers centered on cyber warfare. The March 2026 drone attacks served as a harsh validation that cyber defenses are insufficient — the strikes caused structural damage, disrupted power, and triggered fire suppression systems, highlighting vulnerabilities in physical plant design that were previously theoretical.
The industry is now writing new rules in real time. Here is what the post-2026 data center security framework looks like:
Geographic risk assessment is now mandatory. Every data center location decision must include a geopolitical risk analysis — proximity to conflict zones, exposure to state-level military threats, and the likelihood of being on a future target list.
Single-region redundancy is dead. AWS’s three-zone model failed when two zones were hit simultaneously. Multi-region, multi-provider architecture is now the baseline for resilient enterprise infrastructure.
Physical hardening is no longer optional. Drone defense systems, reinforced structures, and hardened power delivery are moving from nice-to-have to essential infrastructure requirements for any facility in a risk zone.
Migration planning is a board-level discussion. Infrastructure migration — the ability to physically move IT equipment from a high-risk location to a safer one — is no longer an IT team conversation. It is a business continuity conversation that belongs in the boardroom.
India is emerging as a safe haven. For enterprises in the Gulf region and beyond, India’s political neutrality, growing data center infrastructure, and geographic distance from the current conflict zone make it an increasingly attractive destination for infrastructure migration.

9. How One World Logix Helps You Move Infrastructure to Safety
When AWS told its customers to “consider migrating workloads to other regions” after the drone strikes, that advice was for cloud workloads. It said nothing about what to do if you have physical IT infrastructure — your own servers, storage arrays, networking equipment — sitting in a building in Dubai, Abu Dhabi, or Bahrain.
Physical infrastructure cannot be migrated with a few clicks. It needs to be assessed, dismantled carefully, packed using specialized anti-vibration and anti-static methodology, transported by teams who understand both the IT side and the logistics side, and reinstalled and commissioned at the new location — all without losing your data or your operational continuity.
This is what One World Logix has been doing for 14 years, across India and 30+ countries worldwide.
Emergency Site Assessment: Our team can reach your Middle East facility, conduct a full physical inventory and risk assessment, and deliver a complete migration plan within days — not weeks.
Specialized IT Equipment Packing: Servers, storage arrays, and networking hardware require anti-vibration crating, anti-static packaging, and custom protection for precision components. Our packing methodology was developed over 14 years specifically for IT hardware.
Physical Relocation — Dubai to Mumbai, Bahrain to Bangalore: Our Global Field Engineer network operates in UAE, Saudi Arabia, Bahrain, UK, Singapore, Germany, and 25+ other countries. When you need to move infrastructure out of a conflict zone, we have the people and the equipment on the ground to do it.
Reinstallation and Commissioning: We do not stop when the hardware arrives at the new location. Full reinstallation, cable management, system configuration, testing, and sign-off are included. Your systems need to run — not just arrive.
Certified and Compliant: IAM certified, GEM empaneled, MSME registered, ISO 9001:2015 certified. Enterprise and government clients get the compliance documentation they need for high-stakes infrastructure moves.
Final Thought
The 2026 Iran-US conflict has permanently changed the answer to one of the most fundamental questions in enterprise IT: where is my infrastructure, and is it safe?
Data centres are now being treated like oil refineries and power plants — strategic assets that can influence both military operations and civilian life. The concept of “cloud warfare” is emerging, where control over data and digital systems becomes as important as control over territory.
Your data center has an address. That address is now a strategic fact — not just a logistical one.
If your infrastructure is in a region that is on a published enemy target list, the time to act is not after the next strike. It is now.
One World Logix is ready to help you assess your exposure, plan your migration, and execute the physical relocation of your infrastructure to a safer location — anywhere in the world.
📞 +91-882-882-0887 📧 info@oneworldlogix.com 🌐 oneworldlogix.com/owl/data-center-migration/
Get a free emergency site assessment — before your infrastructure becomes a headline.

