Before dawn on March 1, 2026, something happened that nobody in the technology industry had ever seen before.
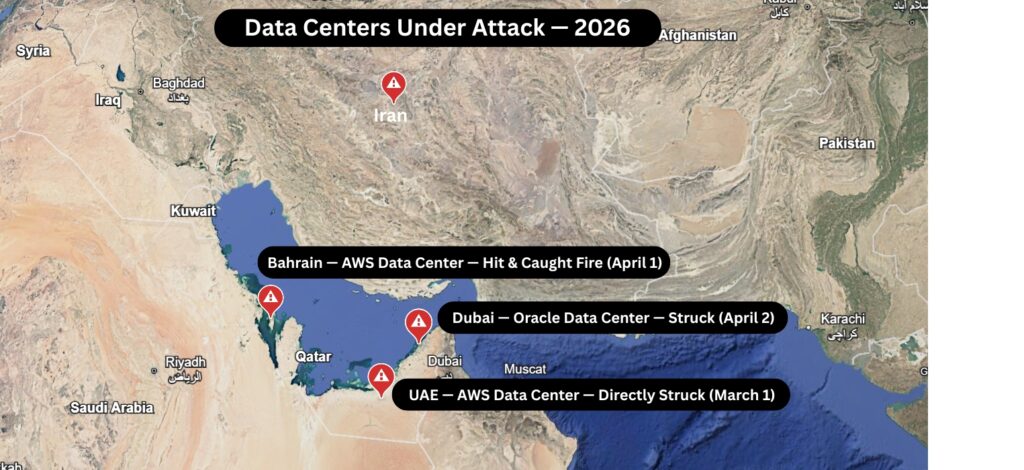
Iranian Shahed drones struck two Amazon Web Services data centers in the United Arab Emirates. A third facility in Bahrain went offline shortly after. Within hours, banks stopped working. Payment apps crashed. Ride-sharing platforms went dark. Enterprise software across the Gulf region simply stopped responding.
This was not a cyberattack. This was not a system failure. This was a physical military strike on commercial data centers — and it worked.
Data center disaster recovery in 2026 is no longer just about power outages and hardware failures. It is about something that most IT leaders never planned for: the possibility that your data center’s address can be found, targeted, and destroyed. This is why understanding Data Center Disaster Recovery 2026 is crucial for all organizations.
If your organization has infrastructure in any geopolitically sensitive region—or even if you don’t—this blog is for you.
Table of Contents
- What Actually Happened — The Iran-AWS Attack, Explained
- The Damage Was Worse Than Anyone Expected
- Why Data Centers Have Become War Targets in 2026
- Who Is Actually at Risk — And It Is Not Just Middle East Companies
- What Traditional Disaster Recovery Plans Completely missed.
- Data Center Disaster Recovery in 2026 — What a Real Plan Looks Like
- How One World Logix Helps You Migrate and Recover, Anywhere in the World
- The Action Steps You Need to Take Right Now

1. What Actually Happened — The Iran-AWS Attack, Explained
Most people heard about this story and moved on. Let’s slow down and understand what actually occurred, because the details matter.
On the morning of March 1, 2026, Iran launched a wave of Shahed drone strikes across the UAE and Bahrain as part of its retaliation in the ongoing US-Iran conflict. Among the targets: Amazon Web Services data centers.
Two AWS facilities in the UAE were directly struck. A third in Bahrain was damaged by a nearby explosion. Iran’s IRGC explicitly claimed responsibility, stating the strikes were intended to target infrastructure that was “supporting the enemy’s military and intelligence activities.”
AWS itself confirmed the attacks on its health dashboard, describing structural damage, disrupted power delivery, and, in some cases, fire suppression systems that flooded the servers with water—causing additional damage on top of what the drones had already done.
Then on April 1, another AWS data center in Bahrain caught fire after a fresh Iranian strike. On April 2, Iran claimed it had also hit an Oracle data center in Dubai.
By that point, the message was unmistakable: data centers are now military targets.
2. The Damage Was Worse Than Anyone Expected
Here is what the attacks actually broke:
AWS’s Middle East region (ME-CENTRAL-1) has three availability zones — three separate physical locations designed so that if one goes down, the others keep everything running. The strikes took out two of those three zones simultaneously. The third was not enough to carry the load.
The services that went offline included EC2, S3, DynamoDB, AWS Lambda, RDS, Kinesis, CloudWatch, and the AWS Management Console itself. These are not minor services. They are the backbone of how thousands of enterprises run their operations.
The businesses that reported disruptions paint a clear picture of what happens when a data center goes down mid-conflict: Abu Dhabi Commercial Bank, Emirates NBD, First Abu Dhabi Bank, payment platforms Hubpay and Alaan, Snowflake, and Careem—the region’s largest ride-hailing platform—all reported significant outages.
AWS later took an extraordinary step: it waived all usage-related charges for the ME-CENTRAL-1 region for the entire month of March 2026. That is how serious the damage was. The cloud giant was essentially admitting that its customers had paid for a service it could no longer deliver.
Recovery, AWS warned, would be “prolonged, given the nature of the physical damage involved.”
3. Why Data Centers Have Become War Targets in 2026
To understand why this happened, you need to understand how much the world has changed in the last five years.
Modern militaries run on AI. The US military uses cloud infrastructure — including AWS — for intelligence analysis, target identification, and operational decision-making. When a data center processes both a bank’s transactions and a military’s AI models in the same building, it stops being a neutral civilian facility. It becomes dual-use infrastructure.
Iran understood this. When it struck AWS, it was not trying to stop people from using Netflix. It was trying to disrupt the AI systems it believed were helping coordinate strikes against Iranian targets.
The broader implication is deeply uncomfortable for every enterprise on earth: the line between commercial cloud infrastructure and military infrastructure has effectively disappeared. And that means data centers—yours, ours, everyone’s—are potential targets in any future conflict.
Iran has already published a list of 17 American technology companies it considers legitimate targets, including Microsoft, Google, Apple, Nvidia, Oracle, IBM, Dell, and Cisco. These are companies whose infrastructure spans the entire globe.
This is the new reality of data center disaster recovery in 2026. Physical attacks are now on the threat matrix.
4. Who Is Actually at Risk — And It Is Not Just Middle East Companies
You might be reading this thinking, We don’t operate in the Middle East, so this doesn’t apply to us.
Think again.
Any company that stores data on AWS, Azure, or Google Cloud has infrastructure in multiple global regions. If you have not specifically checked which regions your workloads run in, there is a real chance some of them are in conflict-adjacent zones.
Indian enterprises with business operations in the UAE, Saudi Arabia, Kuwait, or Bahrain are directly exposed. That is a large number of companies — from BFSI and pharma to IT services and manufacturing.
Beyond geography, there is the supply chain risk. The war has disrupted the Strait of Hormuz, affecting oil flows, and created shortages in helium, aluminum, and LNG—all of which are critical to semiconductor manufacturing. Even if your data center is physically safe, the hardware you need to repair or replace it may become unavailable or dramatically more expensive.
And then there is the cyber dimension. Iranian state-sponsored hacking groups, including MuddyWater, Charming Kitten, and OilRig, have all been activated and are actively targeting critical infrastructure across the US, Gulf states, and allied nations—including India.
Physical strike or not, your data center’s risk profile just changed permanently.
5. What Traditional Disaster Recovery Plans Completely Miss
Most enterprise disaster recovery plans were built for three scenarios: natural disasters, hardware failures, and cyberattacks. They were not built for what happened in the UAE.
Here is what traditional plans get wrong in 2026:
Single-region redundancy is not enough. AWS’s three-zone model was designed to handle one zone going down at a time. A coordinated military strike across multiple zones simultaneously broke the model completely. If your DR plan depends on geographic redundancy within the same country or region, it may not protect you.
Recovery time assumes the damage is recoverable. When a drone hits a server room, you are not dealing with a crashed database or a corrupted file. You are dealing with structural damage, fire, water, and destroyed hardware worth billions of rupees. Recovery is not measured in hours — it is measured in weeks or months.
Insurance does not cover acts of war. Most standard commercial property and business interruption insurance policies explicitly exclude war as a cause of loss. Companies that suffered losses in the UAE attack are now discovering this the hard way.
Your vendor’s plan is not your plan. AWS waived charges. That is not the same as restoring your operations. While Amazon worked on its infrastructure, businesses were offline, losing revenue and customer trust every hour.
Cyber and physical risks are now connected. Iranian drone strikes were coordinated with cyber operations from IRGC-affiliated hacking groups. A physical attack can be a cover for data exfiltration. A cyberattack can disable the systems you need to respond to a physical incident. Your disaster recovery plan needs to address both simultaneously.
6. Data Center Disaster Recovery in 2026 — What a Real Plan Looks Like
A real disaster recovery plan for 2026 needs to be built for a world where physical attacks on infrastructure are possible. Here is what that looks like in practice:
Geographic diversification across conflict-safe regions. Your primary and backup data centers should not both be in the same geopolitical risk zone. If your primary is in the UAE, your backup cannot be in Bahrain. For Indian enterprises, migrating workloads to India-based data centers significantly reduces exposure to Middle East conflict risk.
Multi-cloud and multi-region architecture. Do not put all your workloads in one cloud provider’s region. Distribute across providers and geographies so that a single physical event cannot take you completely offline.
Clear RTO and RPO defined for physical disaster scenarios. Your Recovery Time Objective and Recovery Point Objective need to be tested against the scenario of your primary data center being physically inaccessible — not just offline. How quickly can you be operational from a completely different location?
War risk insurance. If your business has significant cloud workloads in conflict-adjacent regions, speak to your insurance broker immediately about war risk coverage. It exists. Most companies just do not have it.
A pre-qualified migration partner on standby. When disaster strikes, you do not have time to evaluate vendors, negotiate contracts, and coordinate logistics. You need a partner who already knows your infrastructure and can move fast. This is where physical migration expertise becomes critical — and it is exactly what most pure-cloud vendors cannot provide.
Regular physical site assessments. Know where your hardware actually lives. Most enterprises are surprised to learn exactly which physical buildings their cloud workloads run from. You cannot protect what you cannot identify.
7. How One World Logix Helps You Migrate and Recover, Anywhere in the World
At One World Logix, we have spent 14 years doing something that cloud consultants simply cannot do: physically moving IT infrastructure safely, securely, and without disrupting your business.
When AWS told its customers to “consider migrating workloads to other regions” after the drone strikes, that was the cloud-side advice. What it did not cover was what happens to companies who have their own physical IT infrastructure — their own servers, storage arrays, networking equipment — sitting in facilities that are suddenly in a conflict zone.
That physical infrastructure cannot be migrated with a few clicks. It needs to be carefully assessed, packed using specialized anti-vibration and anti-static methodology, transported by teams who understand both the logistics and the IT side, and reinstalled and recommissioned in a new facility — all with minimal downtime.
This is what we do, every day, across India and 30+ countries worldwide.
Here is specifically how One World Logix supports disaster recovery and infrastructure migration in 2026:
Emergency Site Assessment. Our team can reach your facility and conduct a full physical assessment of your IT infrastructure — inventory, dependencies, risk profile — before a single cable is touched. You get a complete migration plan within days, not weeks.
Specialized IT Equipment Packing. Servers, storage arrays, and networking hardware are not like office furniture. Improper packing during transport causes vibration damage, electrostatic discharge, and connector failures that are often not discovered until the equipment is powered back on at the new site. Our packing methodology, developed over 14 years, is built specifically for IT hardware.
Physical Relocation Across India and Globally. Whether you need to move infrastructure from Dubai to Mumbai, from Bahrain to Bangalore, or from any conflict-risk zone to a safer location, our Global Field Engineer network means we have boots on the ground wherever you need us. UAE, Saudi Arabia, UK, Singapore, Germany — we have operated in 30+ countries.
Reinstallation and Recommissioning. Moving hardware is only half the job. Our team handles full reinstallation, cable management, power-up sequencing, and functional testing at the destination site. We do not hand you a pile of equipment and wish you luck.
Parallel Operations Support. For migrations where zero downtime is non-negotiable, we support phased migration approaches — keeping your existing environment running while we bring the new location online, then cutting over in a controlled window.
Certified and Compliant. One World Logix is certified with IAM (International Association of Movers), registered on GEM (Government e-Marketplace), and MSME registered — giving enterprise and government clients the compliance documentation they need for high-stakes infrastructure moves.
8. The Action Steps You Need to Take Right Now
You do not need to wait for a drone to make this a priority. Here is what every IT leader and operations head should do this week:
Map your actual physical infrastructure. Know exactly which buildings your cloud workloads and physical servers are in. Contact your cloud provider and ask for a physical location list of your assigned availability zones.
Review your DR plan for physical attack scenarios. If your plan does not account for a facility being physically inaccessible for weeks or months, update it today.
Check your insurance coverage. Call your broker and ask specifically whether your policy covers acts of war affecting data center infrastructure. Most do not. Find out what it would cost to add war risk coverage.
Assess your geographic risk exposure. If you have infrastructure in the Middle East, Southeast Asia conflict zones, or any region with elevated geopolitical tension, do a risk assessment now — not after an incident.
Identify a migration partner before you need one. Disaster recovery is not the time to start vendor evaluation. Speak to One World Logix now, understand our capabilities, and have a plan ready to execute if your situation changes.
The cloud industry spent a decade convincing enterprises that physical location does not matter. March 1, 2026 proved that it does. It always did.
Your data center has an address. Make sure your disaster recovery plan accounts for what can happen to that address.
One World Logix is ready to help you assess, plan, and execute infrastructure migrations — from conflict-risk zones to safer locations, across India and 30+ countries worldwide.
📞 +91-882-882-0887 📧 info@oneworldlogix.com 🌐oneworldlogix.com
Get a free site assessment today — before you need one urgently.

